Hyper-V Just-Enough-Administration (JEA)
I decided to write series of articles about Securing Windows Server what I frequently do. This is first one in this topic.
Problem Statement:
Company owns virtualization infrastructure with some Virtual Machines. Hyper-V Admins are responsible for overall company virtual machines and have full access to Hyper-V host servers. Together with this admins company has group of other admins that are responsible only for particular Virtual Machines and need control them. In our case this is Monitoring VM. Until JEA there was no easy way of doing this task. It was impossible to give access to particular VMs in Hyper-V for particular users. Thanks to JEA we can accomplish this goal by limiting access to users only to particular commands that they need.
Today I will give an example how this task can be accomplished by using Windows PowerShell Just-Enough-Administration (JEA) functionality.
JEA is available with PowerShell 5.0 and higher. For full functionality, it’s recommended that you install the latest version of PowerShell available for your system. You need to install Windows Management Framework (WMF) 5 update in order to have this functionality on Windows Server 2012R2/2012/2008.
We will do following tasks today:
- Enable a JEA solution on Windows Server 2016
- Create and configure session configuration files
- Create and configure role capability files
- Create a JEA endpoint
- Connect to a JEA endpoint on a server for administration
- View logs
To implement JEA on a computer running Windows Server 2016, you must create an endpoint. To do this, you must create and register two PowerShell script files:
- Session configuration file Script with a .pssc file extension that specifies the name of the endpoint to be created and identifies the role capabilities that should be assigned to specific groups.
- Role capability file Script with a .psrc file extension that specifies what cmdlets and other capabilities should be associated with a particular role.
JEA has functionality to do transaction logging to files to have logs in Eventlog its advised to have PowerShell Script block logging enabled in your environment.
Lets Begin
1. First need to Create PowerShell Module and Manifests and RoleCapability files
# Create a folder for PowerShell module
CD “C:\Program Files\WindowsPowerShell\Modules”
New-Item -ItemType Directory -Path .\SecOpsJEA# Create an empty script module and module manifest.
# At least one file in the module folder must have the same name as the folder itself.
CD “C:\Program Files\WindowsPowerShell\Modules\SecOpsJEA”
New-Item -ItemType File -Path .\SecOpsJEA.psm1
New-ModuleManifest -Path .\SecOpsJEA.psd1 -RootModule “SecOpsJEA.psm1”# Create the RoleCapabilities folder and PSRC file
New-Item -ItemType Directory -Path .\RoleCapabilities
New-PSRoleCapabilityFile -Path .\RoleCapabilities\MonitoringAdminsRole.psrc
Notepad .\RoleCapabilities\MonitoringAdminsRole.psrc
# Create the RoleCapabilities folder and PSRC file
New-Item -ItemType Directory -Path .\RoleCapabilities
New-PSRoleCapabilityFile -Path .\RoleCapabilities\MonitoringAdminsRole.psrc
Notepad .\RoleCapabilities\MonitoringAdminsRole.psrc
We should have following structure as a result of above commands:
2. Edit Role Capabilities file to accomplish our goals:
At least one .psrc file called role capabilities file must be created which contains all cmdlets and external programs which will be permitted to use in the JEA session. For this test I’ll create the file which will permit our Monitoring Admins Start/Stop/Restart/Suspend/Resume of one particular Virtual machine which is called “Monitoring” and additionally I give access to PING and WHOAMI commands. User should not have rights to control other VMs.
3. Create and edit session configuration file (.pssc file)
In session configuration file we will define our AD Users Groups and Assign them appropriate Roles by matching Role Capability file which we created earlier. i will create Session configuration file with -Full switch to see all the possible options that it can have. But this is not actually neccessary for our todays goal.
#Create a session configuration file
New-PSSessionConfigurationFile -SessionType RestrictedRemoteServer -Path .\MonitoringAdminsEndpoint.pssc -Full
Notepad .\MonitoringAdminsEndpoint.pssc
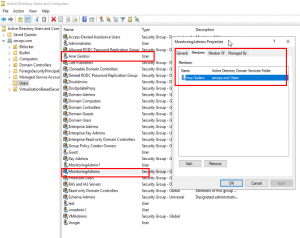
In the following example I match our AD “SecOps\MonitoringAdmins” Security group to our Role capability file called “MonitoringAdminsRole”.
I leave Transcript Logging directory as defaul to C:\Transcipts. About all other parameters you can check offical JEA documentation. We must Import Hyper-V module in our Session in order o be able to fine grain control commands.
After our file is ready we can test it with following command
#Test a session configuration file
Test-PSSessionConfigurationFile -Path .\MonitoringAdminsEndpoint.pssc
4.Creating JEA Endpoint
As a final part of our configuration we need create JEA endpoint which will be used for connections by registering our Sessions Configuration file. Sometimes its neccessary to restart WinRM service after this task. We will aslo check whether our endpoint is successfully registered by listing endpoints on our system.
#Registering JEA Configurations
Register-PSSessionConfiguration -Path .\MonitoringAdminsEndpoint.pssc -Name ‘JEAMonitoringAdmins’ -Force#It maybe neccessary to restart WinRM service for configurationt to get applied
Restart-Service -Name WinRM#List the names of the endpoints on a system
Get-PSSessionConfiguration | Select-Object Name | Format-List
5 Using Endpoint
Now we need to connect to our endpoint on HOST02 server from another computer and test our JEA endpoint using user account AD [email protected] which is the member of SECOPS\MonitoringAdmins secuirty group.
#Testing JEA Endpoint
$NonAdminCred = Get-Credential
Enter-PSSession -ComputerName Host02 -ConfigurationName JEAMonitoringAdmins -Credential $NonAdminCred
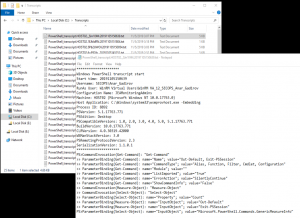
In below example as you see user is able to Restart Monitoring VM but unable to control othe VM which is Database. He is also able to run other assigned commands as WHOAMI and Get-VM.Goal is accomplished.
6. Checking Logs
In our example Transcript Logs are stored in “C:\Transcipts” as it was configured in our Session Configuration file:
For more infor on JEA Configuration please check JEA Documentation page on Microsoft. Its very comprehensive and I advice you to read it for better understanding of the topic. There are many guides about JEA but this particual guide is focused on Hyper-V VM management which myself needed much. To be honest I struggled little in order to figure our some parts of this configuration. Particularly without importing Hyper-V module you are not able to write fine grained Cmdlets by using hash tables. Actually you write them but then don’t work until you import Hyper-V module.
To be more precise following commands work without importing Hyper-V module but it doesn’t give you control over parameters and values when you configure them in Role Capability file:
VisibleCmdlets = ‘Get-VM’, Start-VM’
But following dont. You need to import Hyper-V module in your Session Configuration Filea as I did in Step 3.
VisibleCmdlets = @{ Name = ‘Get-VM’; Parameters = @{ Name = ‘Name’} },
@{ Name = ‘Start-VM’; Parameters = @{ Name = ‘Name’; ValidateSet = ‘Monitoring’ } }
You can get Configuration Steps and Module Directory from my Github Page: