Configuring Ubuntu SSH server to use Hashicorp Vault OTP
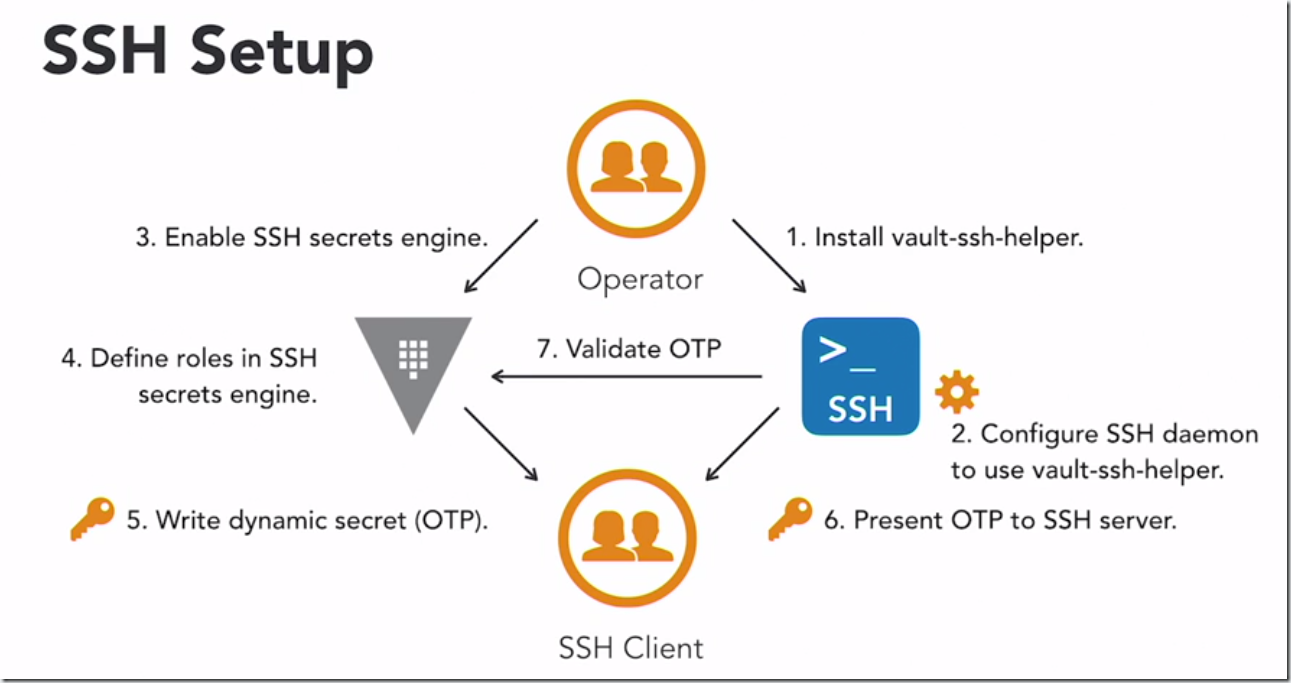
This post will demonstrate how to configure vault and ssh server in order to use OTP for the login to SSH server. Following diagram depicts the process.
After we have initialized and unsealed our vault server we need to enable ssh secrets engine with the following command:
vault secrets enable ssh
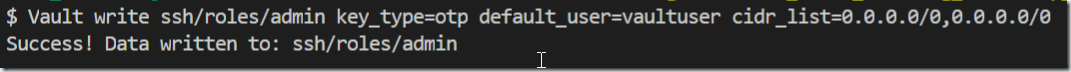
Write role to Vault ssh secrets engine. For the test purposes we will allow all IPs
Vault write ssh/roles/admin key_type=otp default_user=vaultuser cidr_list=0.0.0.0/0,0.0.0.0/0
Now we need to configure login to SSH server install vault ssh helper and modify SSH server config to use OTP from Vault for user login
We will run following script to download and install ssh helper:
#!/bin/bash
#TEST: vault-ssh-helper -dev -verify-only -config=/etc/vault-ssh-helper.d/config.hcl
export VAULT_ADDR=http://vaultserver:8200
wget https://releases.hashicorp.com/vault-ssh-helper/0.1.4/vault-ssh-helper_0.1.4_linux_amd64.zip
unzip vault-ssh-helper_0.1.4_linux_amd64.zip
mv vault-ssh-helper /usr/local/bin
rm vault-ssh-helper_0.1.4_linux_amd64.zip
We need to change SSH server config file by commenting and adding following lines of code to it.
#@include common-auth
auth requisite pam_exec.so quiet expose_authtok log=/tmp/vaultssh.log /usr/local/bin/vault-ssh-helper -dev -config=/etc/vault-ssh-helper.d/config.hcl
auth optional pam_unix.so not_set_pass use_first_pass nodelay
vaulthelper config file:
vault_addr = "http://vaultserver:8200"
ssh_mount_point = "ssh"
tls_skip_verify = true
allowed_roles = "*"
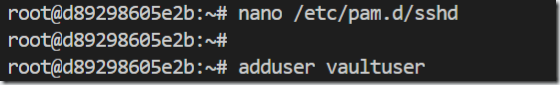
We also need to create user named vaultuser
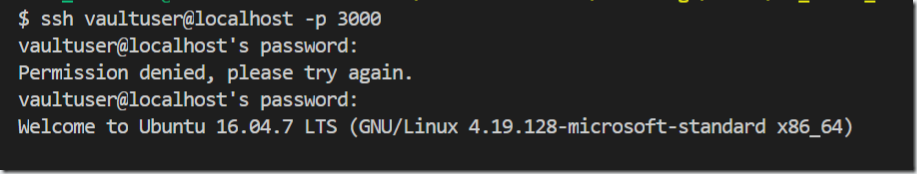
SSH server configuration is ready and the last step is to request OTP from vaul server in order to login to SSH server under user name vaultuser using OTP. IP is the IP of the SSH server.
vault write ssh/creds/admin ip=172.16.238.20
Finally we can use key (OTP) to login to SSH server. Please note that this key is one time and after first login it expires and we are unable to use it anymore.